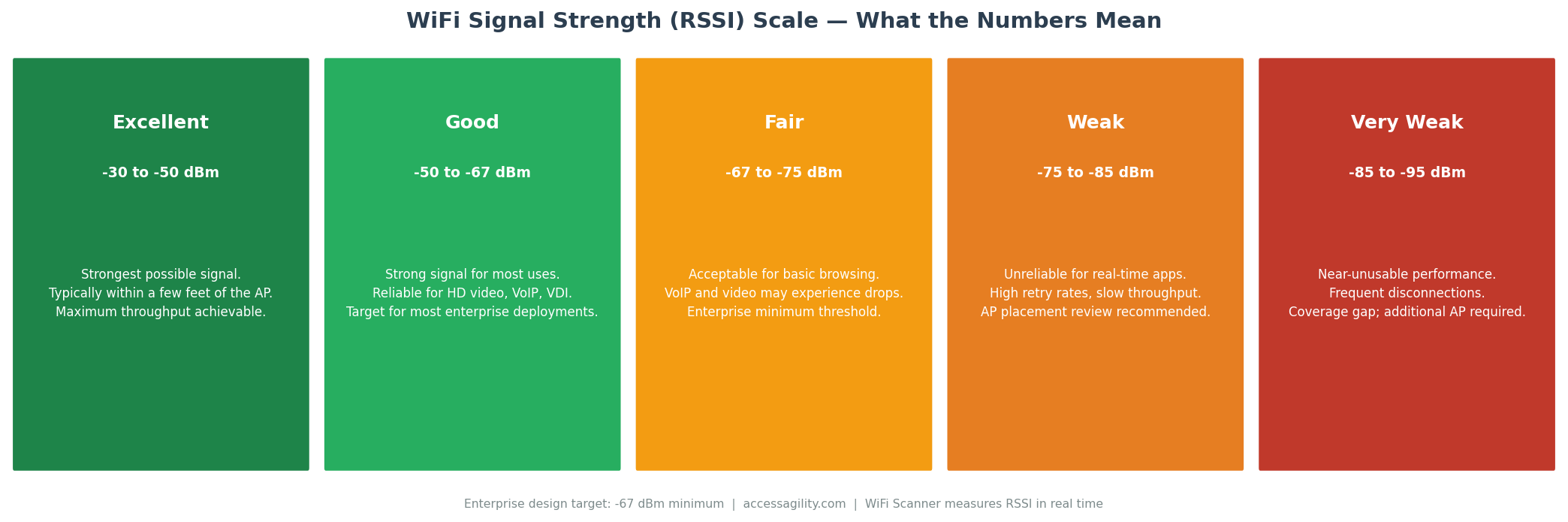
Your laptop shows full WiFi bars, but video calls are still choppy. Your phone shows -85 dBm, but someone says that's fine. What does any of it actually mean? WiFi signal strength measurement is more nuanced than most IT professionals realize — and misunderstanding it leads to poor deployment decisions. Here's what the numbers actually tell you.
WiFi Signal Strength Explained: What the Numbers Actually Mean
[fa icon="calendar'] Mar 16, 2026 6:55:31 PM / by Blog Team posted in WiFi
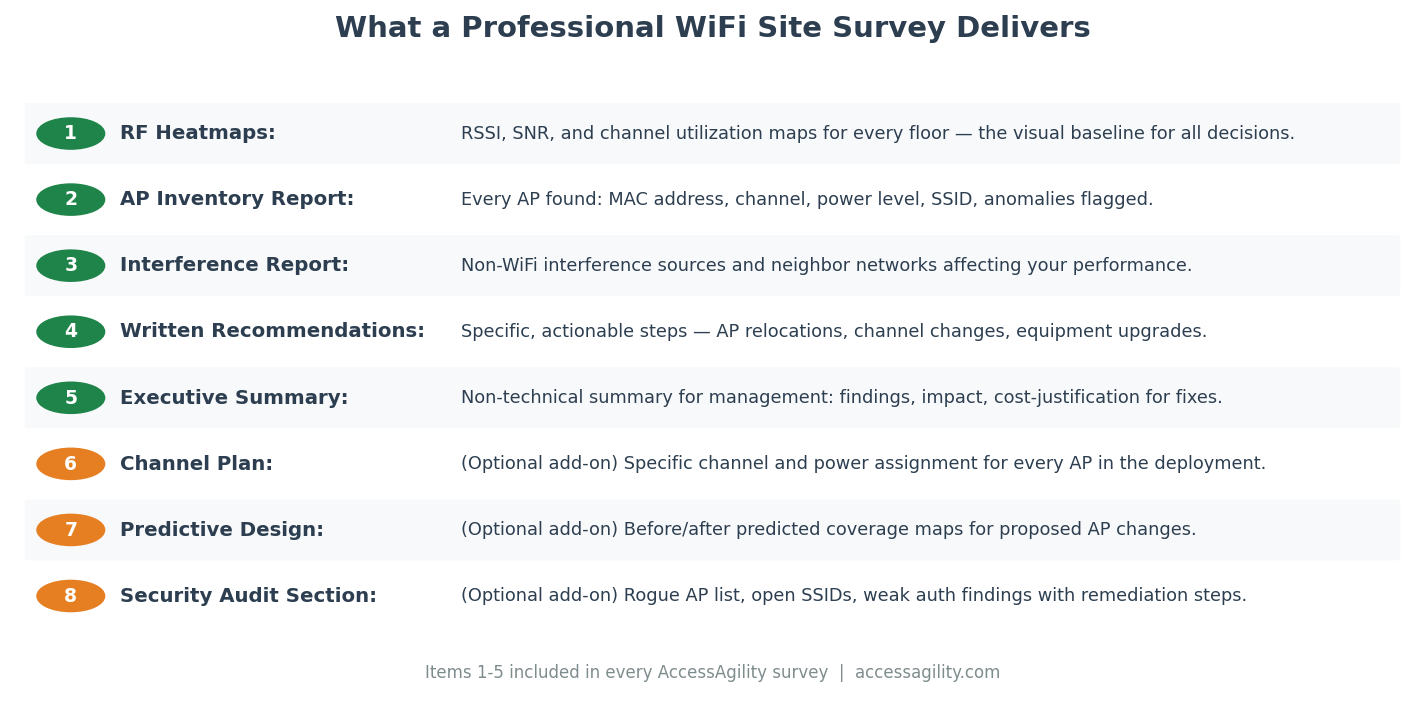
What's Included in a Professional WiFi Site Survey? A Full Breakdown
[fa icon="calendar'] Mar 16, 2026 6:54:29 PM / by Blog Team posted in WiFi
Before you hire a WiFi site survey provider, you need to know exactly what you're buying. "Site survey" means different things to different vendors — and a low-cost survey that delivers a three-page PDF is not the same as a professional engagement that gives you a full RF characterization of your facility. Here's a complete breakdown of what a professional WiFi site survey should include.
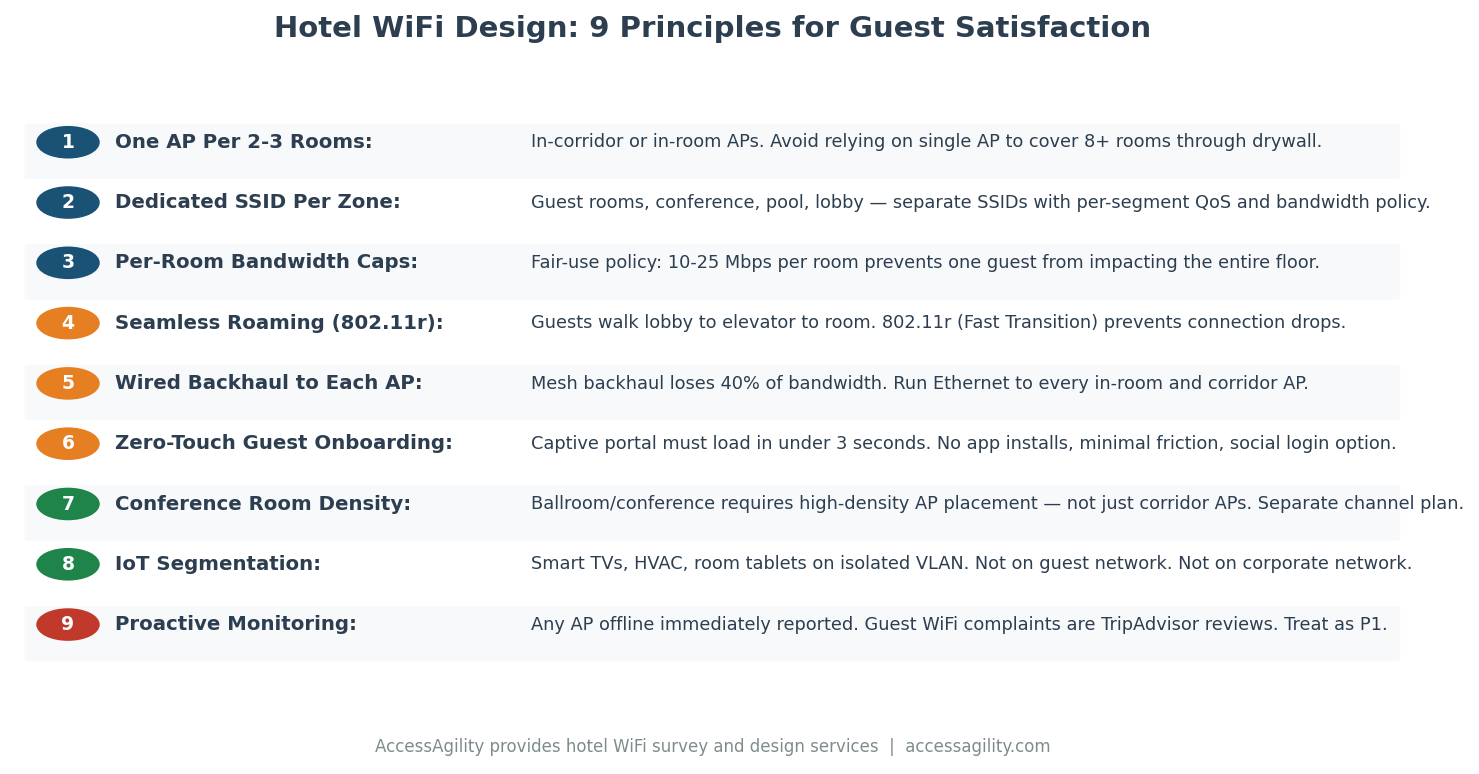
How Hotels Can Deliver the Guest WiFi Experience That Earns 5-Star Reviews
[fa icon="calendar'] Mar 16, 2026 6:53:42 PM / by Blog Team posted in WiFi
WiFi is consistently ranked as the top amenity factor in hotel guest satisfaction surveys — ahead of breakfast, ahead of the fitness center, and in many surveys, ahead of the bed itself. A guest WiFi experience that earns five stars requires the same engineering discipline as enterprise IT WiFi, applied to a uniquely challenging environment with unique user expectations. Here's what it takes to get there.
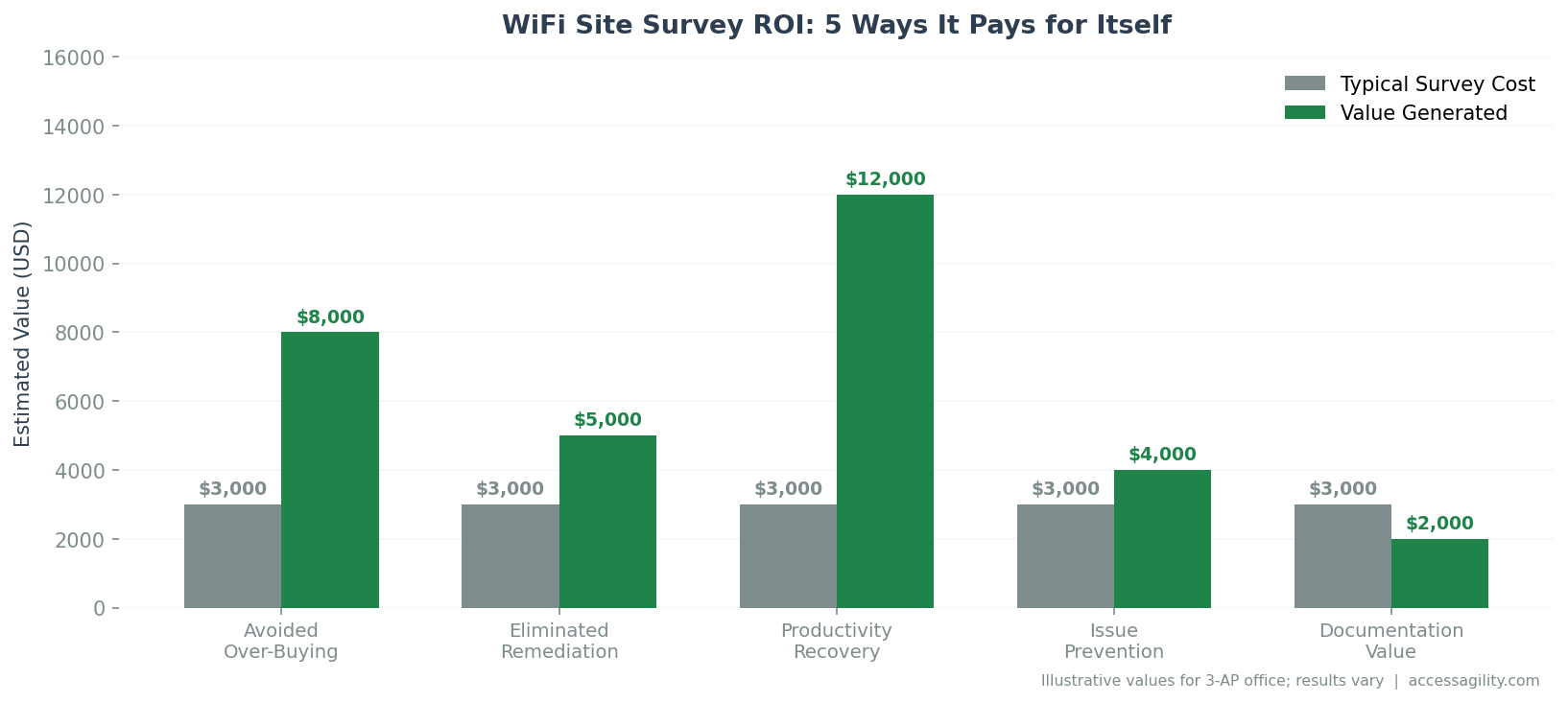
5 Ways a Wireless Site Survey Pays for Itself
[fa icon="calendar'] Mar 16, 2026 6:52:43 PM / by Blog Team posted in WiFi
A professional WiFi site survey is a line item that budget-holders sometimes question. Here's the case that every IT manager should be able to make: a site survey isn't a cost — it's the cheapest insurance policy you can buy against a far more expensive outcome.
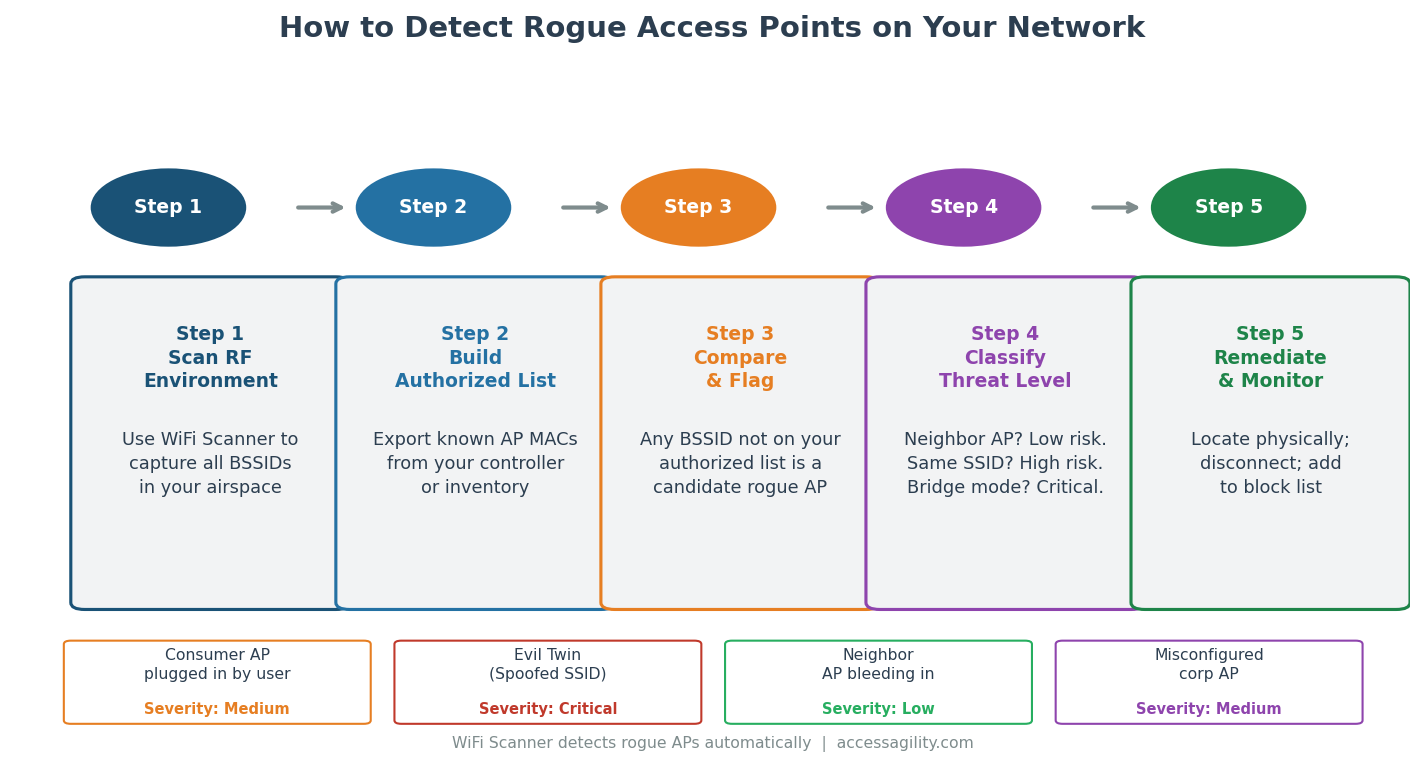
How to Detect Rogue Access Points on Your Network
[fa icon="calendar'] Mar 16, 2026 5:47:02 PM / by Blog Team posted in WiFi
A rogue access point is any wireless AP operating on your network — or in your airspace — that hasn't been authorized by your IT team. Rogue APs are one of the most common WiFi security vulnerabilities, and they're hiding in more enterprise environments than most IT managers realize. Here's how to find them and what to do about them.
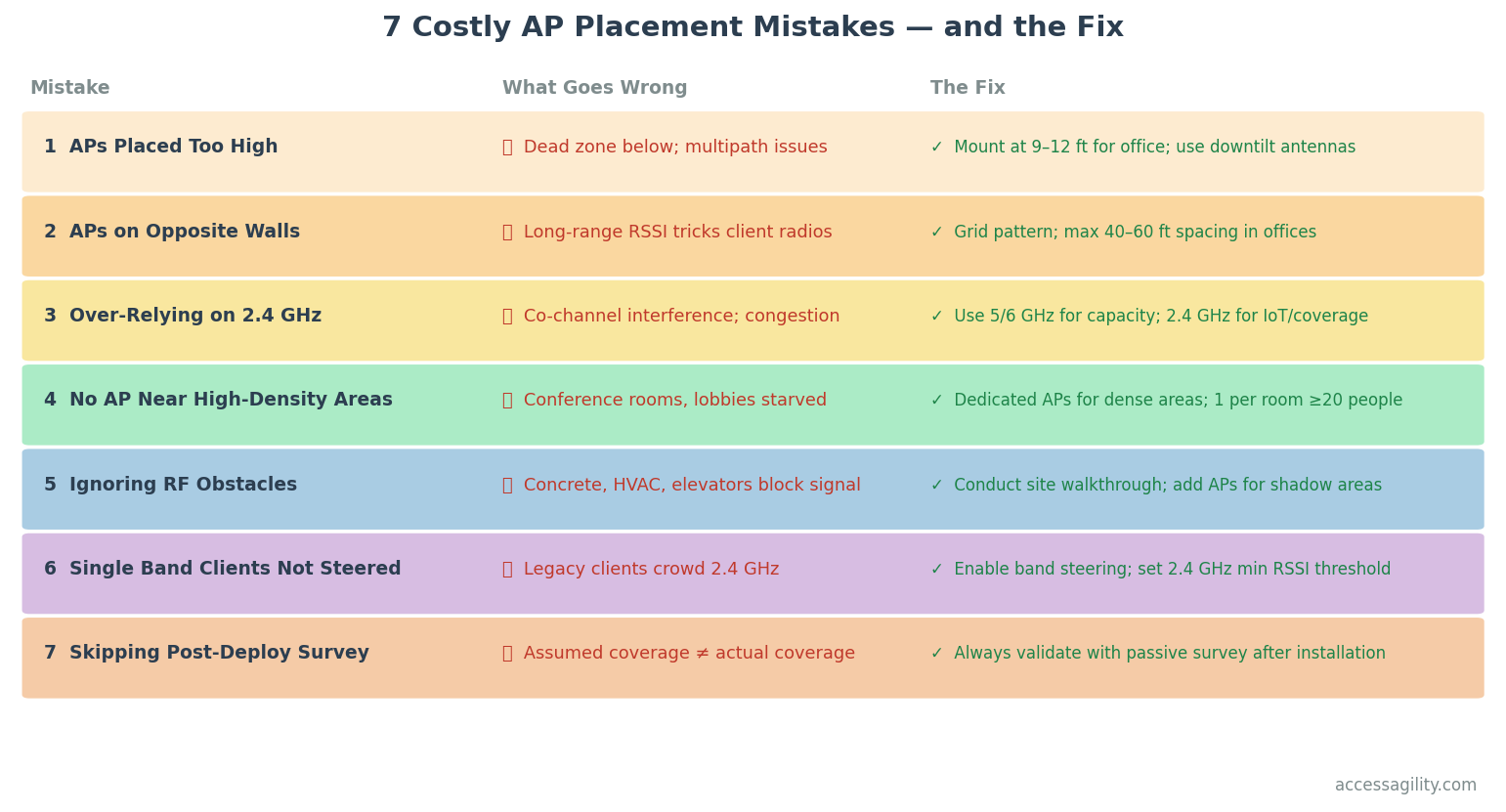
The 7 Most Costly Access Point Placement Mistakes (and How to Avoid Them)
[fa icon="calendar'] Mar 16, 2026 5:45:50 PM / by Blog Team posted in WiFi
Access point placement decisions are permanent once the cable is run and the ceiling tile is closed. A poorly placed AP network can underperform for years before anyone connects the symptoms to the root cause. These are the seven AP placement mistakes that cost enterprises the most — in performance, in remediation time, and in hardware dollars wasted.
4 RF Design Challenges Every IT Manager Faces in 2026 (and How to Solve Them)
[fa icon="calendar'] Mar 16, 2026 5:44:12 PM / by Blog Team posted in WiFi
WiFi 6E access points are now mature enterprise products. WiFi 7 is entering the market. And yet RF design — the practice of planning how radio signals will actually behave in your building — remains the single biggest source of enterprise WiFi failures. Here are the four RF design challenges that IT managers are most likely to encounter in 2026, and the practical steps to address each one.
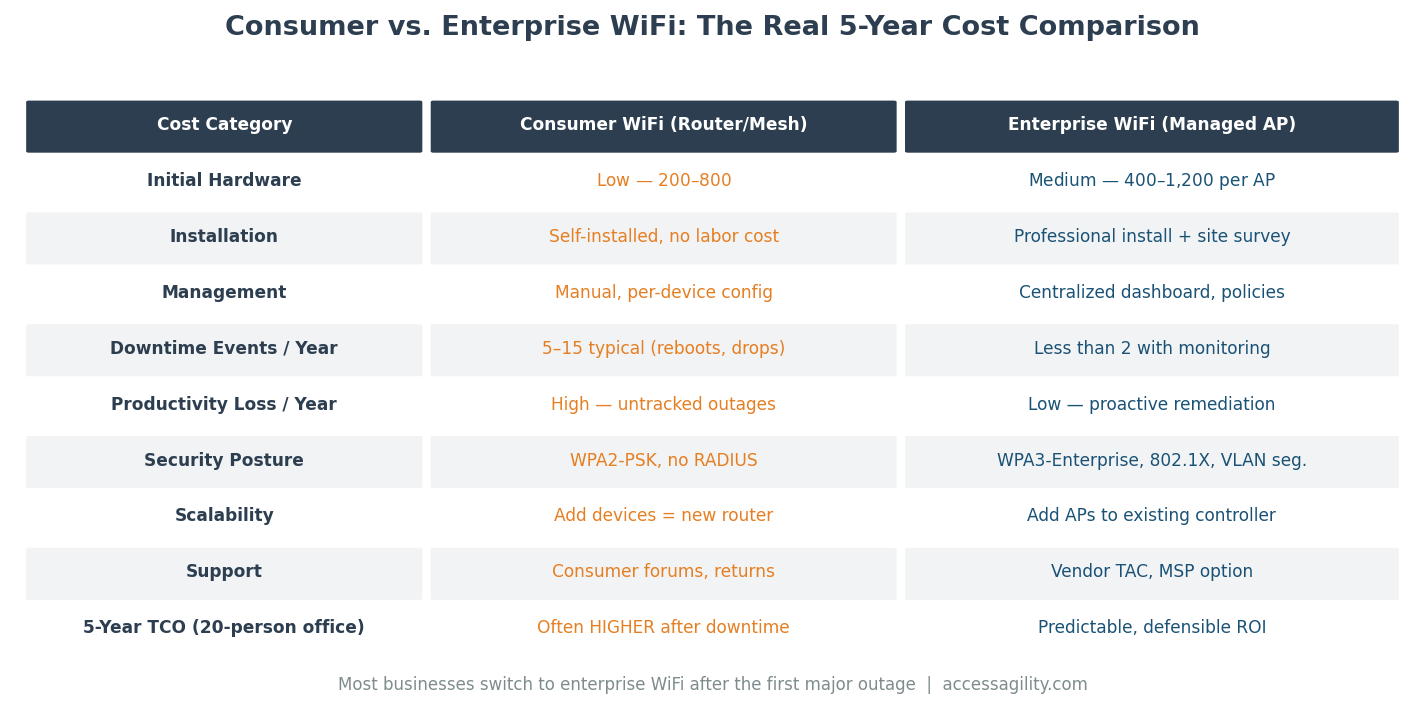
Why Consumer-Grade WiFi Is Costing Your Business More Than You Think
[fa icon="calendar'] Mar 16, 2026 4:51:09 PM / by Blog Team posted in WiFi
Every year, thousands of businesses deploy consumer-grade WiFi routers and access points because they're cheaper than enterprise hardware. It feels like a reasonable cost decision. It isn't. Consumer-grade WiFi creates productivity losses, security exposures, and support costs that routinely exceed the hardware cost savings multiple times over. Here's the real math.
Why Conference Room WiFi Fails — and How to Fix It With Proper RF Design
[fa icon="calendar'] Mar 16, 2026 4:47:51 PM / by Blog Team posted in WiFi
Conference room WiFi is the most visible WiFi problem in any organization. When a video call freezes during a client presentation, or when the CEO's laptop won't connect during a board meeting, the IT team hears about it immediately. Conference rooms consistently rank as the #1 WiFi complaint in enterprise IT surveys — and the root causes are specific, predictable, and fixable.
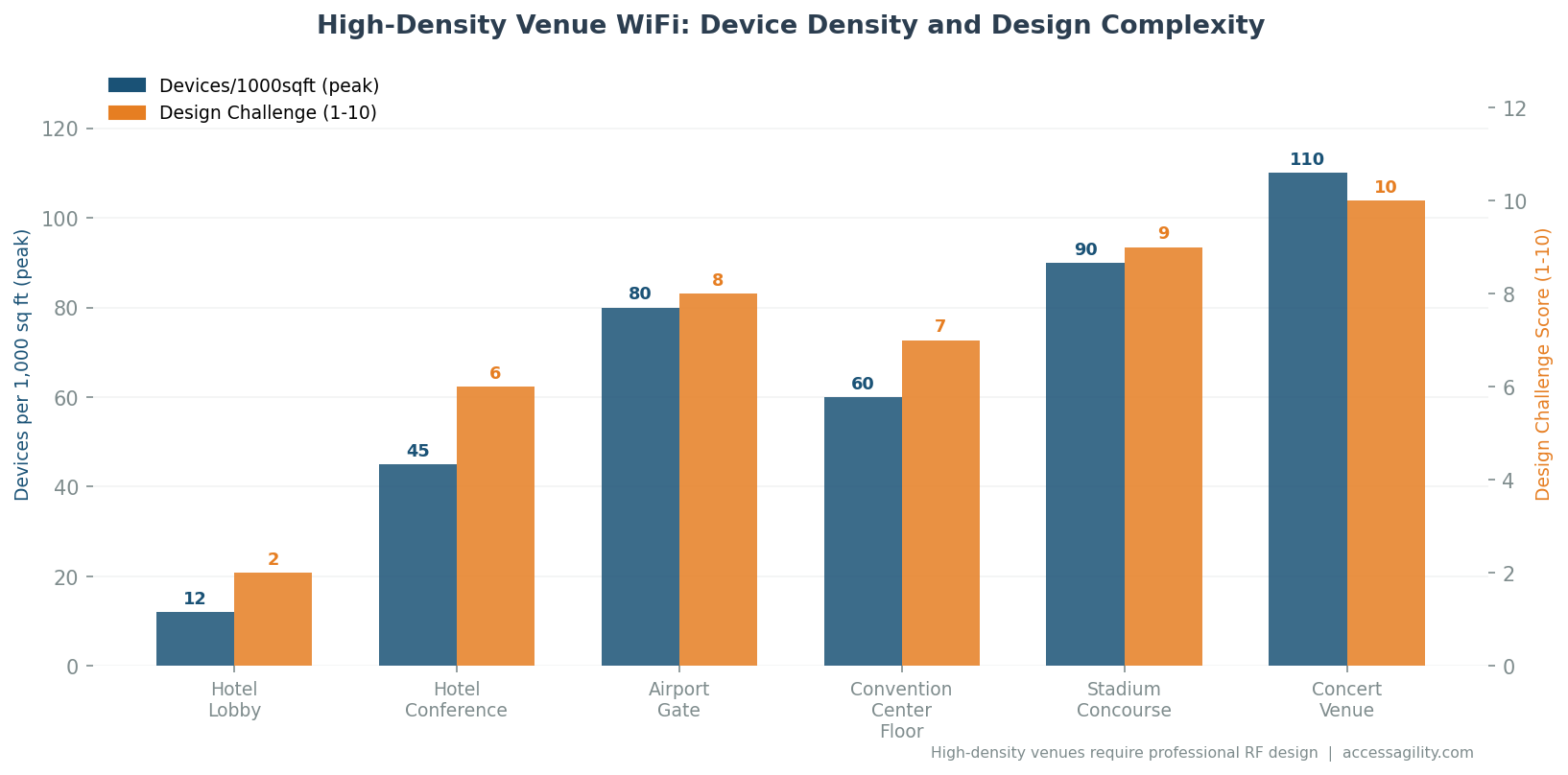
Why Airport and Convention Center WiFi Fails — and the Design Fixes That Work
[fa icon="calendar'] Mar 16, 2026 4:44:06 PM / by Blog Team posted in WiFi
Airport and convention center WiFi failures are some of the most visible WiFi problems in the world. Tens of thousands of people simultaneously attempting to connect their devices, upload photos, join calls, and stream content — in a building whose WiFi was almost certainly designed for a fraction of that concurrent load. Here's why large public venue WiFi fails so predictably, and the design approaches that actually work.