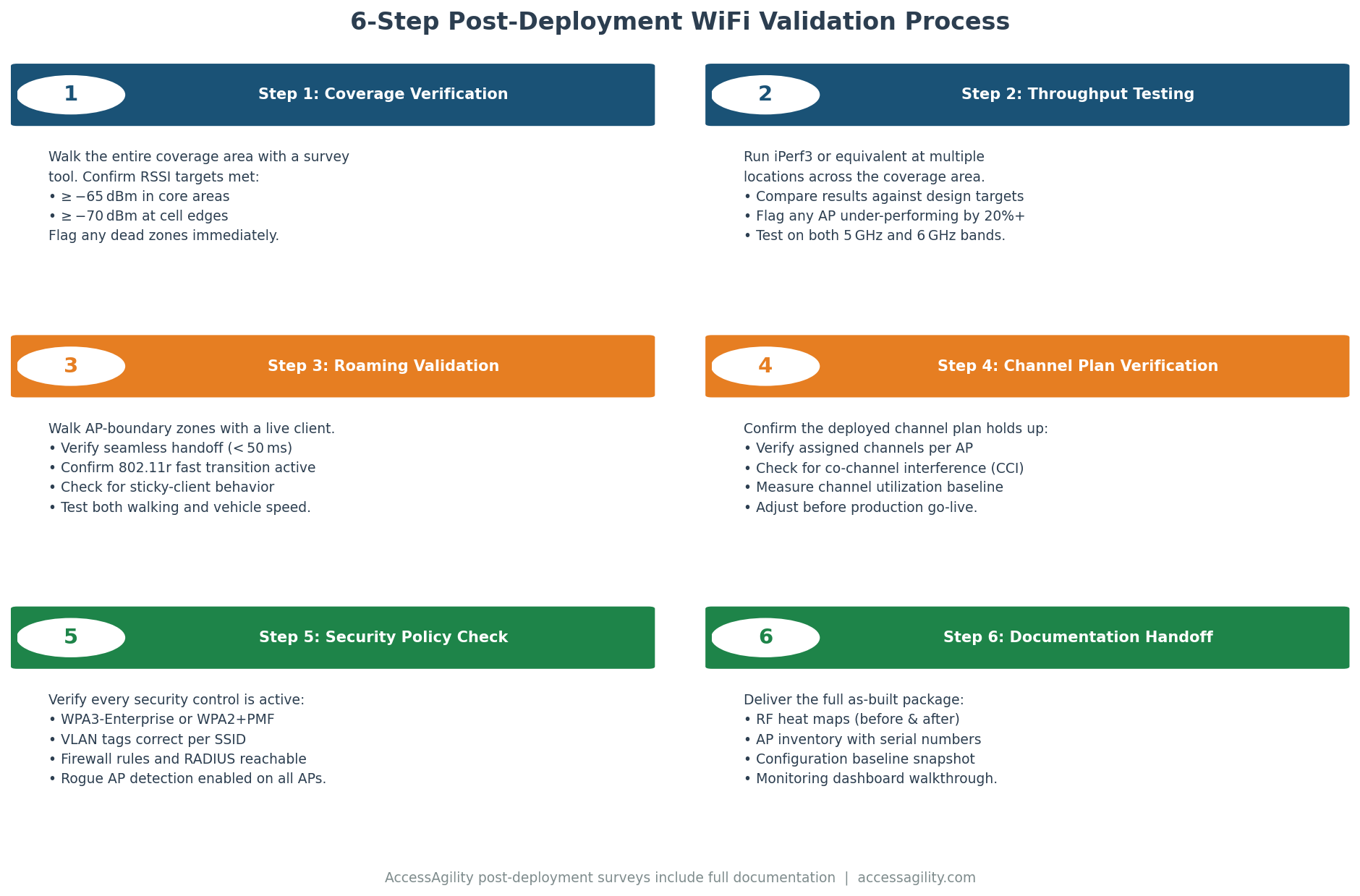
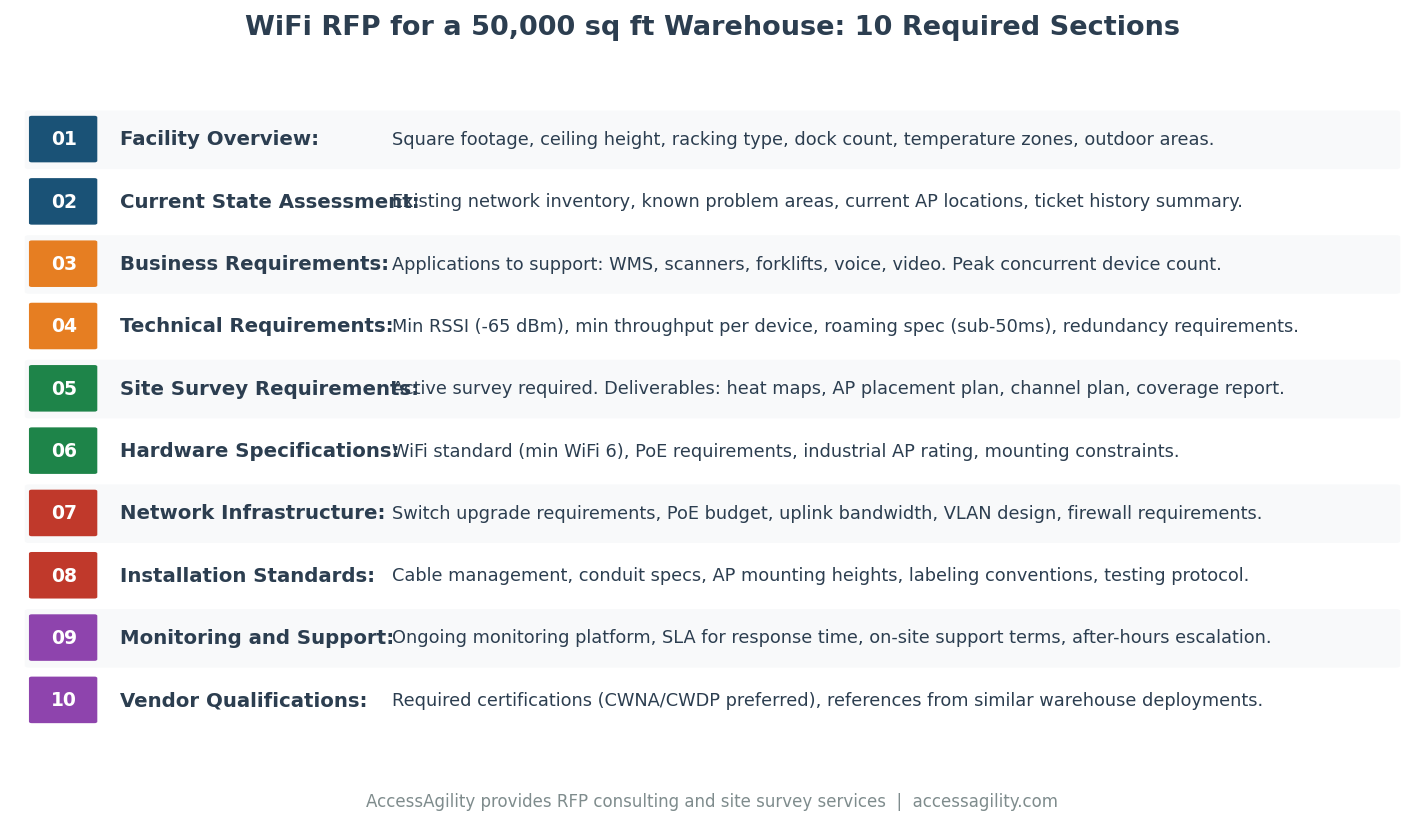
The most expensive WiFi deployment mistake isn't the wrong AP model or a bad channel plan — it's skipping the post-deployment validation survey. Every WiFi installation should be formally validated before it goes into production. Here's exactly how to run a post-deployment WiFi validation survey and what it needs to cover.