PCI DSS 3.2 and 4.0 Standard
The Payment Card Industry Data Security Standard is a worldwide information security standard assembled by the Payment Card Industry Security Standards Council (PCI SSC). The standard was created to help organizations that process card payments prevent credit card fraud through enhanced security measures. The standard applies to all organizations which hold, process, or pass cardholder information from any card branded with the logo of one of the card brands.
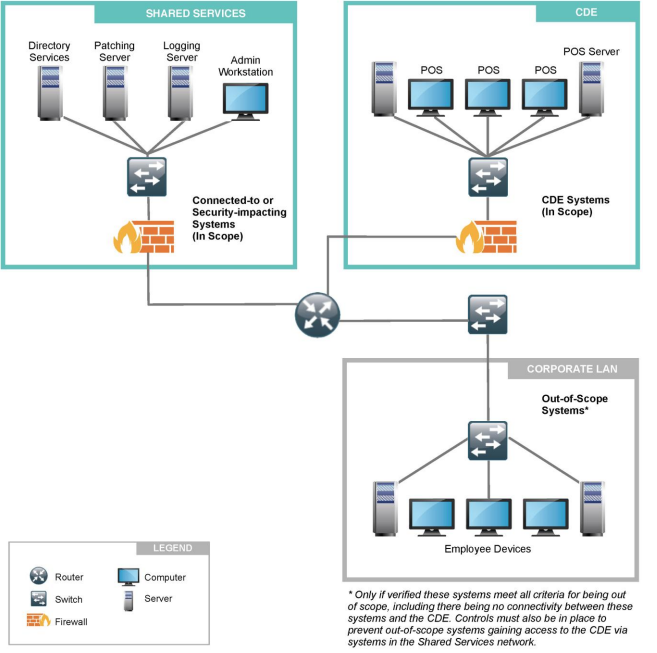
When scoping an environment for PCI DSS, it is important to always start with the assumption that everything is in scope until it is verified that all necessary controls are in place and are actually providing effective segmentation. Effective segmentation can greatly reduce the risk of CDE systems being impacted by security weaknesses or compromises originating from out-of-scope systems.
Network Segmentation and PCI Compliance
PCI audits can be expensive and time-consuming, especially when the audit scope includes your entire network infrastructure. PCI DSS security requirements apply to all system components, where “system components” are defined as “any network component, server, or application that possesses cardholder data or sensitive authentication data. Network components include but are not limited to firewalls, switches, routers, wireless access point, network appliances, and other security appliances.
One way that the scope of a PCI audit can be reduced is through network segmentation. Network segmentation, or isolation of the cardholder data environment (CDE), from the remainder of the corporate network is not a PCI DSS requirement. However, it is recommended as a means of reducing the scope and cost of a PCI DSS assessment as well as a means of reducing general risk to the organization.
If your wireless network is not being used to transmit sensitive cardholder data, then the wireless network can potentially be segmented from the CDE, removing the wireless network from the scope of a PCI audit. There are two ways to achieve this segmentation; locating the WLAN on a completely separate wired network infrastructure that is not connected to the CDE, and using firewall segmentation.
Wireless Network Not Connected to CDE
Segmentation can be achieved by locating the wireless network on a completely separate, parallel wired network that is not connected to the CDE at all. The access points cannot be connected to any switches, routers or other wired infrastructure that is connected even peripherally to the CDE. In addition, the wireless network must have its own Internet connection (ie. it cannot share a modem or firewall with the CDE network).
Firewall-Segmented Wireless Network Connected to CDE
If the wireless LAN is connected to the CDE, it can still be segmented from the CDE if it is separated from the CDE with a firewall according to the following PCI-DSS requirement:
"1.2.3 Install perimeter firewalls between any wireless networks and the CDE, and configure these firewalls to deny or control (if such traffic is necessary for business purposes) any traffic from the wireless environment into the CDE."
Firewall Segmented Cardholder Data Environment (CDE)
VLANs and Network Segmentation
Virtual local area networks (VLANs) cannot be relied upon for network segmentation (eg. having the CDE on one VLAN and the WLAN on separate VLANs) and will not necessarily take the wireless out of the PCI DSS scope. Hackers can potentially hop across VLANs using known techniques if adequate access controls between VLANs are not put in place.
WiFi Scanning Options
The PCI DSS v3.2 and 4.0 standard describes clear requirements for building compliant wireless LANs. Most business class wireless solutions offer a means of achieving PCI compliance. A enterprise class wireless lan solution typically has integrated mapping, logging, and rogue AP detection tools.
If these enterprise features are not available in installed WiFi network solution then a standalone option is to use a laptop based WiFi scanning tool.


